Protecting student data privacy is a never-ending, always-changing job for schools and districts. The challenge they face is that: they’re typically understaffed with limited resources dedicated to cybersecurity, students possess valuable personally identifiable information (PII) that cybercriminals seek, and cyber-attacks continue to advance in sophistication
In this guide, we’ll look at what student privacy is and ways you can improve your student data security.
What Is Student Data Privacy?
Student data privacy is the protection of sensitive student information within a K-12 education system through proper handling and usage. That sensitive data, which can be digital or physical (paper-based), is referred to as personally identifiable information (PII) and includes personal, academic, and behavioral data.
To protect student data privacy, schools, districts, education software companies, and individual users must adhere to policies and practices that protect information from unauthorized access, misuse, or disclosure. Proper protection ensures that PII is collected, stored, used, and shared securely and responsibly while complying with student data privacy laws and regulations.
K-12 Security Tips That Will Protect Student Data Today
Thank You!
You should receive a confirmation email shortly with a link to the resource you requested. If you don’t receive it within 10 minutes, please check your spam folder.
To get the full eBook right now, please click on the button below.
What’s the Difference Between Student Data Privacy and Student Data Security?
Student data privacy and student data security go hand in hand. Student data privacy refers to the protection of sensitive student PII from unauthorized access, misuse, or disclosure through proper handling and usage. Student data security also focuses on data protection, but through technical and organizational measures.
Data security safeguards student information against risks that include data breaches, hacking attempts, malware, ransomware, phishing attacks, or physical theft. Schools and districts can improve their data security measures with strict access controls, encryption techniques such as MFA (multi-factor authentication) and M2FA (multi-factor data encryption), firewalls, system updates, and staff, student, and parent training on cybersecurity best practices.
What Are Examples of Student Personally Identifiable Information (PII)?
A student’s personally identifiable information (PII) refers to data that identifies or distinguishes that individual student. PII is sensitive and should be handled carefully to ensure privacy and security.
Examples of student PII include basic information like a student’s full name, student ID number, social security number (SSN), date of birth, physical or mailing address, phone number, or email address. Additional PII includes gender, ethnicity or race, health information, family information, and academic records, such as grades, test scores, attendance records, disciplinary records, and transcripts.
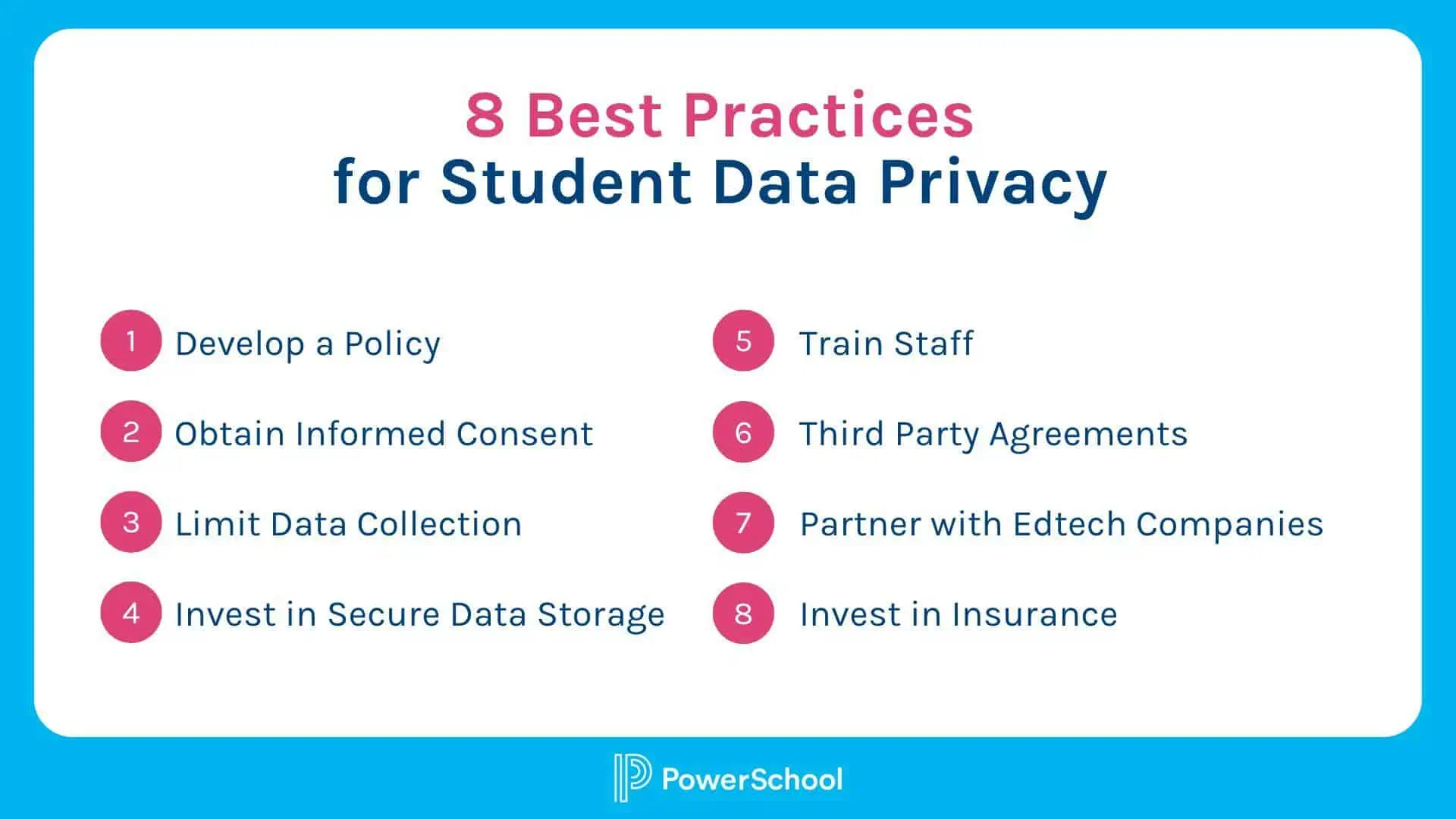
8 Best Practices for Student Data Privacy
While no one can eliminate cyber threats and attacks or make their districts 100% safe from student data privacy breaches, we can take steps to improve data privacy and security. Here are key recommendations for best practices:
- Develop a Comprehensive Student Data Privacy Policy: Create a clear privacy policy that outlines how student data is collected, used, stored, and shared. Communicate the rights of students, the purposes for which data is collected, and the measures in place to protect their information.
- Obtain Informed Consent: Obtain appropriate consent from parents or legal guardians before collecting student data. Inform parents of their rights regarding data privacy.
- Limit Data Collection: Collect only the necessary data directly relevant to a student’s education. Minimize the collection of unnecessary personal information and regularly review data collection practices to ensure compliance with privacy laws.
- Secure Data Storage and Sharing: Robust data security measures are critical to protecting student data from unauthorized access. Encrypt data both at rest and during transmission, use secure storage systems, and regularly back up data. Restrict data access to only those users who have to have it and implement strong authentication protocols.
- Train Staff on Data Privacy: Current and ongoing training is needed for all levels of staff, students, and even parents. Training helps build and fortify your human firewall and improve your users’ ability to spot and prevent cybersecurity attacks.
- Maintain Third-Party Use Agreements: When sharing student data with third-party vendors or service providers, establish clear agreements that outline data protection obligations, limitations on data usage, and data breach notification requirements. Conduct due diligence to ensure that third parties have appropriate security measures in place.
- Partner with Vetted, Reliable Edtech Vendors: Choose edtech partners with products that meet TrustedEd App from 1EdTech certification, which ensures the product is vetted and can support your data privacy and security protection needs. Other vendor features that help ensure data privacy include industry-leading security protocols, security by design, end-to-end encryption, third-party penetration testing, intrusion detection, auditing, and mandatory training. Also, look for interoperability between a vendor’s edtech products through standards that ensure secure data sharing.
- Purchase Cybersecurity Insurance: Cyber coverage insurance policies can help mitigate the financial and reputational risks from cyber attacks and data breaches that threaten student data privacy. These policies, often called “cyber liability insurance” or “data breach insurance,” are specifically designed to address the unique risks and challenges faced by schools and districts.
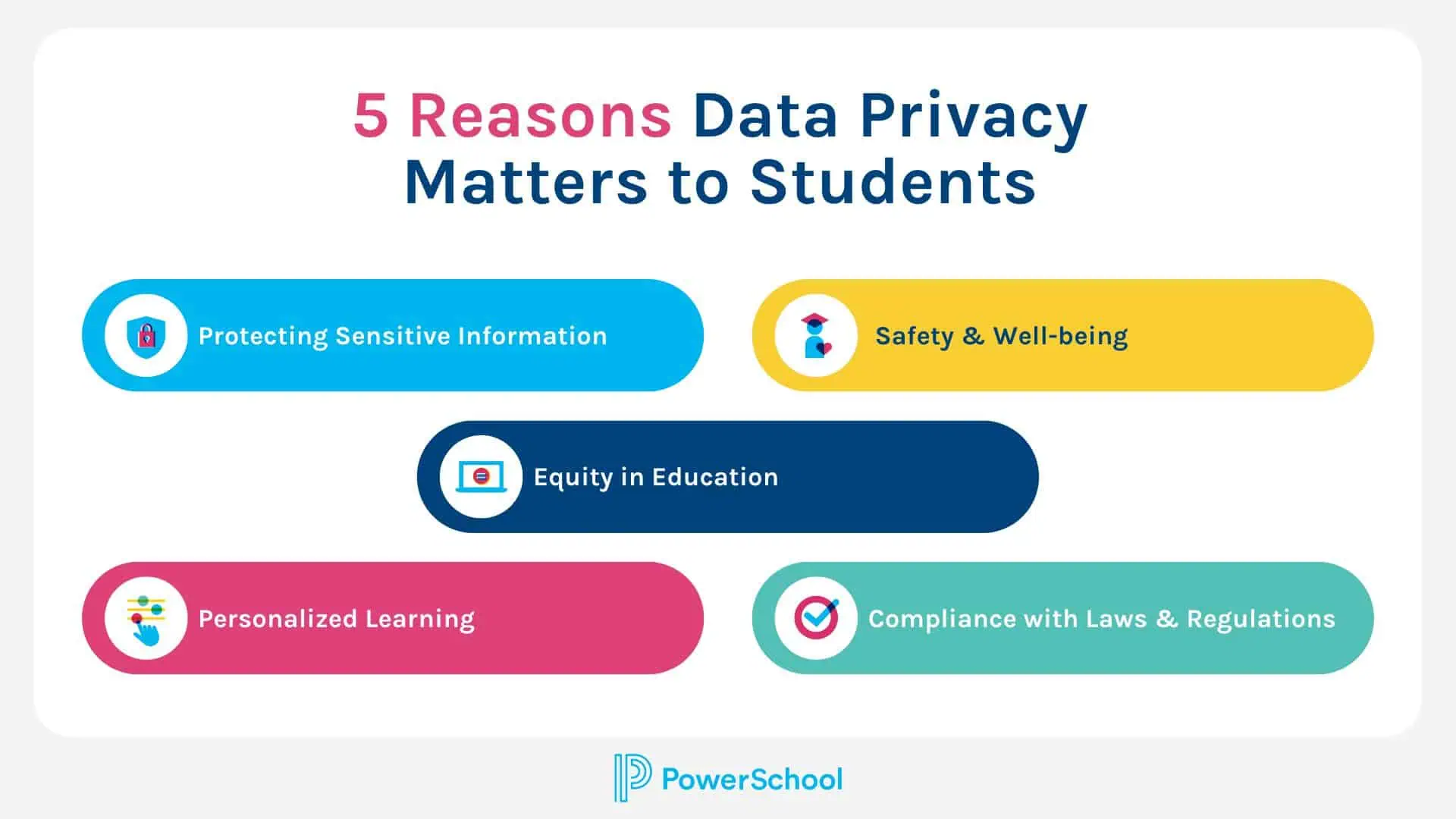
5 Reasons Why Data Privacy Is Important to Students
According to the U.S. Dept. of Education, the value of a student record on the black market is $250 to $350. Protecting their data privacy is essential for both their potential as a vulnerable target and for maintaining the integrity and safety of their education journey. For example, a single cyberattack creates a loss of student learning of up to three weeks, and the overall recovery time for an attack, in general, is up to nine months, with the average recovery time for a ransomware attack at 287 days.
Here are some reasons why data privacy is crucial for K-12 students:
- Protecting Sensitive Information: K-12 students often have limited control over their personal information, including names, addresses, and academic records. Data privacy safeguards their sensitive information from unauthorized access, misuse, or disclosure.
- Safety and Well-being: Data privacy helps create a secure environment where students can learn, interact, and express themselves without fear of exposing or misusing their personal information. It contributes to their psychological safety, allowing them to confidently explore and develop their skills and talents.
- Equity in Education: Data privacy helps ensure student data is used fairly and without creating biases or discrimination. It helps protect students’ privacy rights and prevents data misuse that could lead to unfair treatment, tracking, or labeling based on sensitive information.
- Personalized Learning: Data privacy is critical in data-driven insights to tailor instruction and provide personalized learning experiences. It ensures that student data is used only for legitimate educational purposes and that any data analysis or profiling is conducted in a manner that respects privacy rights and maintains student anonymity when necessary.
- Compliance with Laws and Regulations: Schools and districts must comply with privacy laws and regulations. Adhering to these regulations protects the rights of K-12 students and their families.
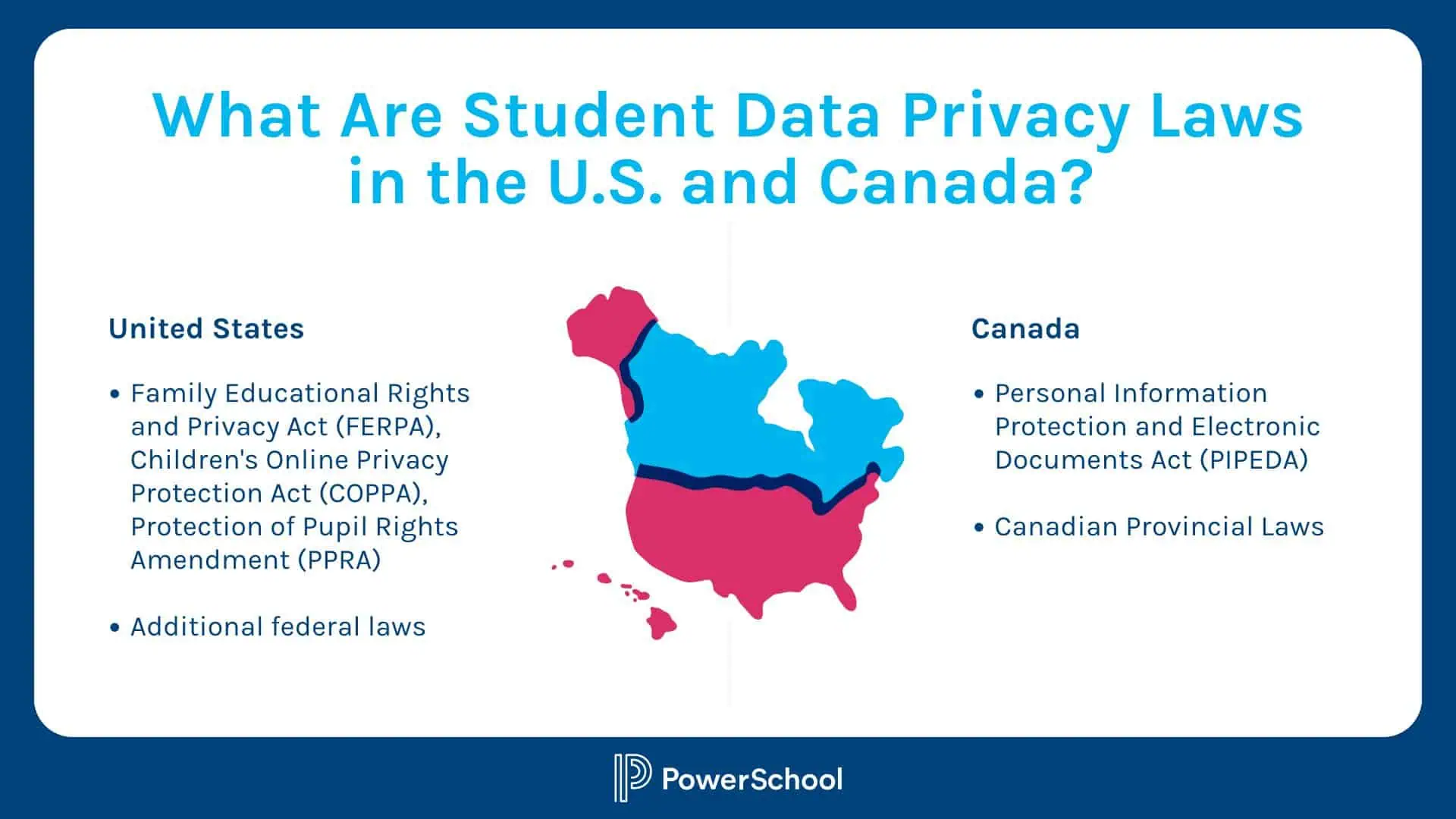
What Are Student Data Privacy Laws in the U.S. and Canada?
In the U.S. and Canada, several key laws and regulations that address student data privacy are administered and enforced by national education departments. Here are some of the most widely recognized federal ones:
United States:
- Family Educational Rights and Privacy Act (FERPA) protects the privacy of student education records, granting parents and students rights around the access and control of their education records. It also restricts the disclosure of PII from education records without consent.
- Children’s Online Privacy Protection Act (COPPA) applies to online services directed toward children under 13. It requires operators of websites or online services, including education technology vendors, to obtain verifiable parental consent before collecting, using, or disclosing personal information from children.
- Protection of Pupil Rights Amendment (PPRA) applies to the collection of personal information from students for use in surveys, analyses, or evaluations. It ensures parents know and consent to their students’ participation when collecting sensitive information like political beliefs, religion, or sexual behavior.
- Additional federal laws include General Data Protection Regulation (GDPR), Breach Laws, Data Residency Laws, the Digital Millennium Copyright Act (DMCA), the Sarbanes-Oxley Act, and state contracts for reporting.
Canada:
- Personal Information Protection and Electronic Documents Act (PIPEDA): This federal law governs the collection, use, and disclosure of personal information by private-sector organizations, including educational institutions. It applies to the handling of student data by educational institutions across most of Canada.
- Canadian Provincial Laws: Some Canadian provinces have their own privacy legislation that specifically addresses student data privacy. Examples include the British Columbia Freedom of Information and Protection of Privacy Act (FIPPA) and the British Columbia Personal Information Protection Act (PIPA).
Key Features to Look for in a Student Data Privacy Platform?
Cybersecurity threats to student data privacy continue to rise, so it’s critical to ensure you’re partnering with edtech platform vendors that prioritize student data security. When choosing or re-evaluating your edtech partners, make sure you work with vendors that are transparent in their cybersecurity and data privacy policies and practices.
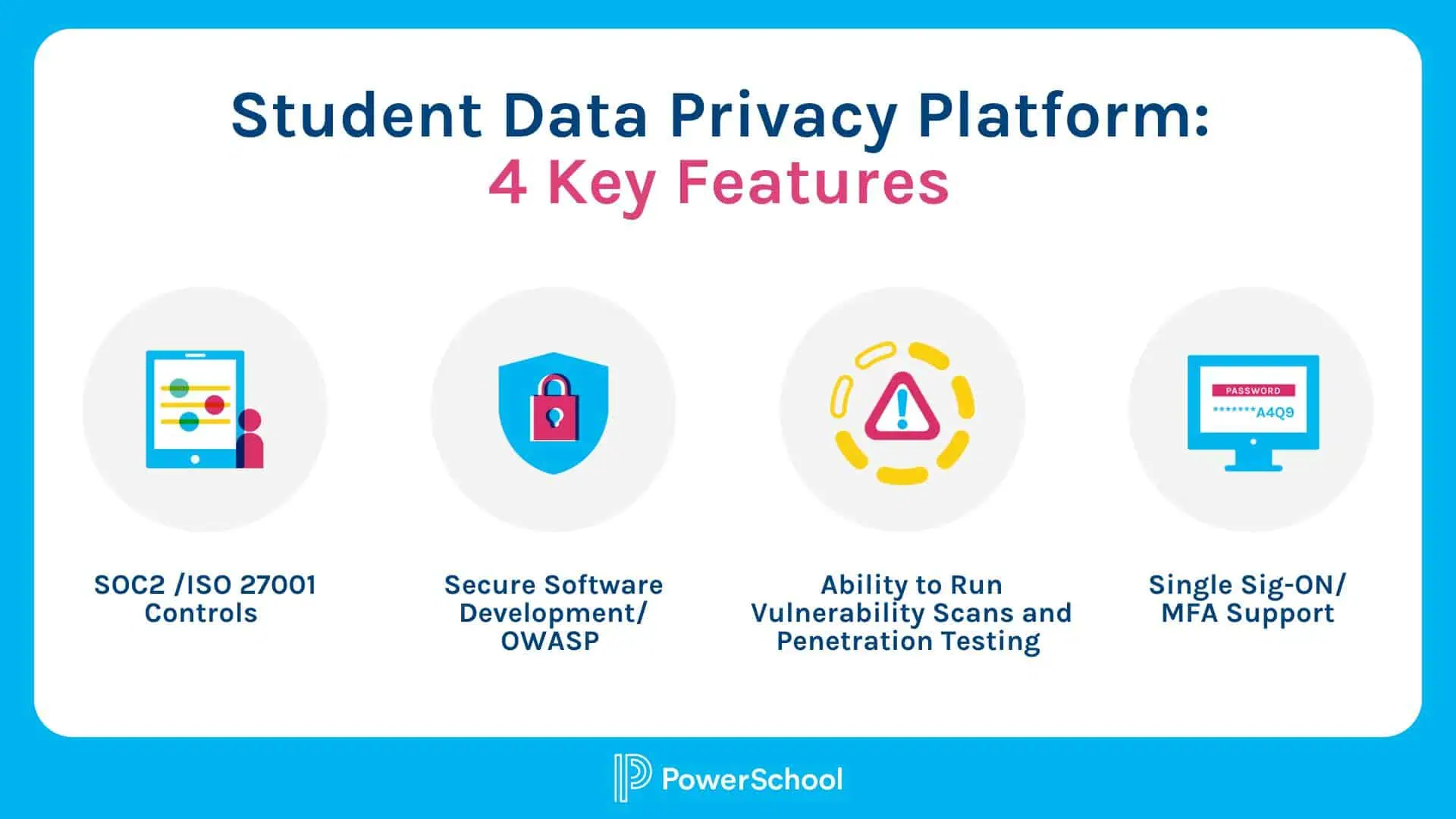
Here are key features to look for in a student data privacy platform:
- Penetration Testing/Vulnerability Scans—penetration tests should be conducted by independent testers at least annually, and vulnerability scanning is done continuously as part of development
- ISO 27001/SOC 2 Controls—ensuring software is adequately tested before deployment and that robust security and privacy practices are in place
- Secure Software Development/OWASP—confirming security is considered in the entire process of developing software, including training, code reviews, and vulnerability end-to-end scanning
- Single Sign-On (SSO)/Multifactor Authentication (MFA) Support—for advanced security, product platforms should support SSO integrations with an external identity where MFA can be enabled for an additional layer of security

20-Point Cybersecurity Inspection for Edtech Vendors
Put your edtech vendor to the test in this 20-point cybersecurity inspection.
Take the TestHow PowerSchool Provides Superior Student Data Privacy and Security
A leading provider of K-12 education technology solutions, PowerSchool is committed to being a good custodian of student data—taking all reasonable and appropriate countermeasures to ensure data confidentiality, integrity, and availability. The company believes that the safe collection and management of student data is essential to student success within the 21st Century digital classroom.
PowerSchool certifies its software solutions’ application, database, and infrastructure security. Customers own their student and school data; PowerSchool has no rights to access or sell student or school data. It does not collect, maintain, use, or share student personal information beyond that needed for authorized educational or school purposes or as authorized by the parent or student.
PowerSchool has signed the national Student Privacy Pledge regarding the collection, maintenance, and use of student personal information. The pledge states: “School service providers take responsibility to both support the effective use of student information and safeguard student privacy and information security.”
Additional security measures and infrastructure of PowerSchool include:
- Privacy, security policies, and infrastructure are tested and validated continually by credible industry-leading third parties and align with state and federal regulations
- Dedicated security team led by a chief information security officer
- SOC 2 compliance. To minimize risk and exposure to customers’ data, PowerSchool receives annual SOC 2 Type 2 examinations on the company’s controls relevant to security, availability, and confidentiality for multiple applications.
- Security Operations Center (SOC). Security and maintenance responsibilities are on us as the cloud provider, and we take them very seriously. Our Security Operations Center runs 24x7x365, providing “eyes on glass monitoring and response” to security issues on an organizational and technical level.
- ISO 27001:2013 certification. PowerSchool performs annual third-party audits of its security management system and has achieved the internationally recognized ISO 27001:2013 certification. The ISO 27001 certification outlines standards with annual, third-party audits that evaluate processes, trainings, and more.
- Penetration testing/vulnerability scans. PowerSchool performs vulnerability scanning regularly in software development to ensure any vulnerabilities are found and fixed before being shipped. The company completes static, dynamic, and software composition analysis as part of SDLC and regular third-party penetration testing.
- Next-generation end-point protection on all servers and devices
- Real-time vulnerability scanning on all servers
- Web Application Firewall (WAF) and Intrusion Detection System/Intrusion Protection System (IDS/IPS) to protect networks and devices.
- Secure software development/OWASP—confirming that security is considered in the entire end-to-end process of developing software, including training, code reviews, and vulnerability scanning
- Customer data handling—ensuring data residency, with no information going offshore, and strict policies and processes to handle data safely
- Security awareness training. Extensive and ongoing security/cybersecurity training is required of all employees, along with secure coding training for software engineers.
This blog and content (Content) is a proprietary resource owned exclusively by PowerSchool. The Content is protected under international copyright conventions. Use of this Content does not of itself create a contractual relationship, create any warranty between PowerSchool and any person. PowerSchool expressly disclaims any and all liability to any person who may view the Content. The Content is presented for informational purposes and not offered as professional advice for any specific matter.
Tips for Creating a Successful K-12 Cybersecurity Plan
Get practical tips and best practices for how to create a K-12 cybersecurity plan to better protect your student, staff, and school data.
Read the Blog